Zero-Knowledge Proof is a cryptographic method by which one party, “the prover” can prove to another party “the verifier”, that certain statements are true without revealing any other information.
One of the core traits of blockchain is transparency, but when dealing with sensitive data, a certain level of privacy and security is needed. Let’s say you are at a pub, and you are asked to prove that you are of legal age. You may be hesitant to give information other than your age. What could you do?
This is where Zero Knowledge Proofs (ZKP) come into play. The ZKP protocol has a close connection to cryptography.
So, what exactly is ZKP? Zero-knowledge proof is a unique method that involves two parties: the prover and the verifier. The prover proves to the verifier that they know something about x without conveying any information that they know the value of x.
As per the above example, let’s say the pub wants to know if you are over 21 years old. In ZKP, the bartender (the verifier) requests proof that you are over the age of 21. You give the bartender your ID, just showing your age without revealing any other information.
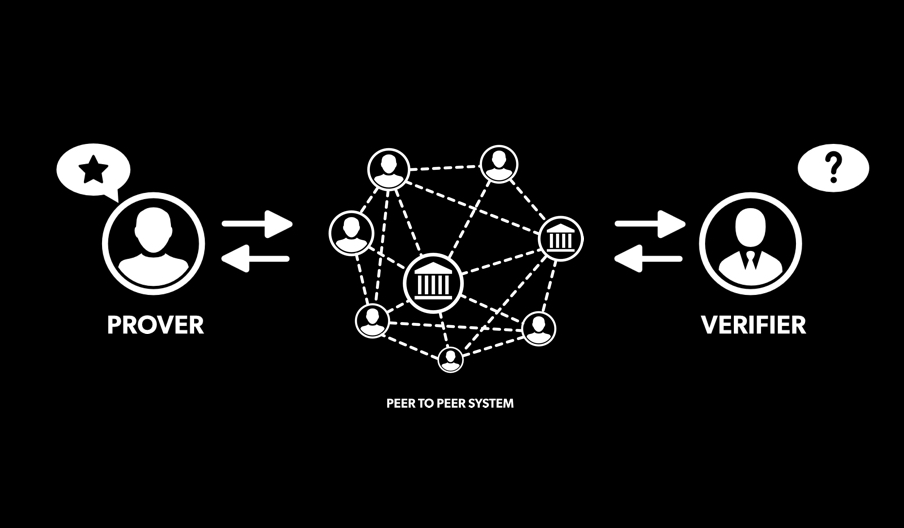
ZKPs are one of the most fascinating concepts in applied cryptography. They could be used to provide anonymous and secure transactions for public blockchain networks, which is the core strategy of zero-knowledge-proof applications.
A zero-knowledge proof must satisfy three parameters
- Completeness
If “x” is true, the verifier will be convinced of this fact by an honest prover. - Soundness
If “x” is false, the prover can convince you that it is true, though the probability is very small. - Zero-knowledge
If the statement is true, no Verifier learns anything other than that it is true. In other words, just knowing the statement is sufficient to imagine a scenario, showing that the prover knows the secret. This is achieved by each verifier having a simulator, which can produce a transcript that “looks like” an interaction between the prover and the verifier. The simulator should be able to produce the transcript, while only having access to the statement to be proved and not the prover itself.
Hence, zero-knowledge proofs are probabilistic proofs rather than deterministic ones, as there are chances that the prover can prove a false statement as true to the verifier. However, there are a few tools available to reduce soundness to negligible levels.
General Structure of ZKP
There are three actions: Witness, Challenge and Response
Witness
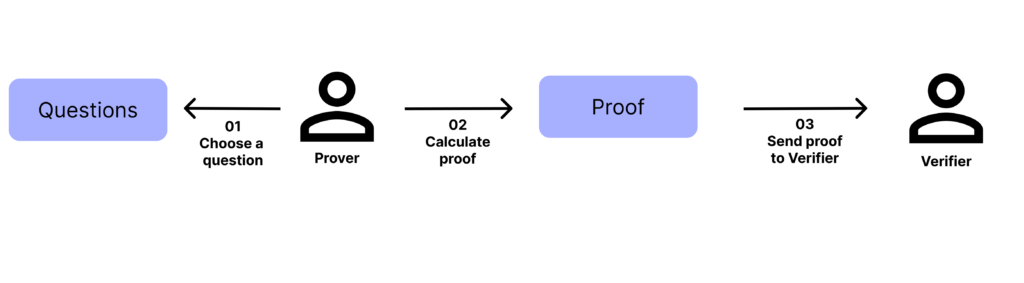
Fig: Prover picks a random question and sends the proof to the verifier
Challenge
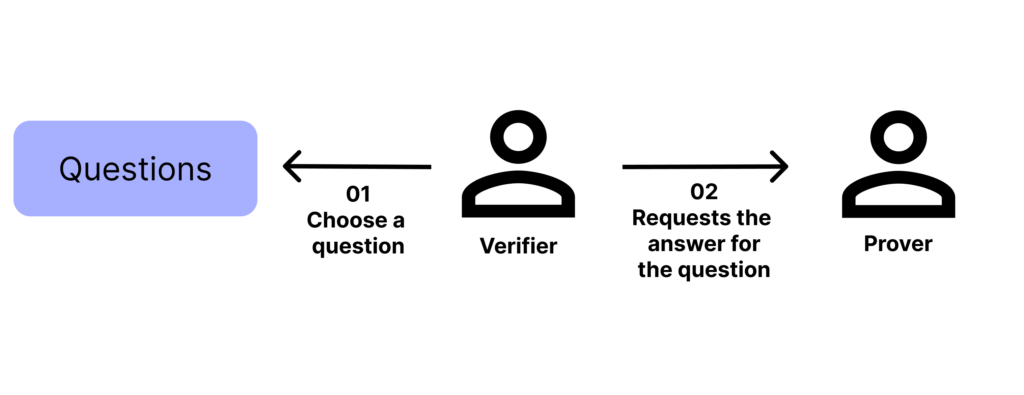
Fig: Verifier picks a question and asks the prover to answer
Response
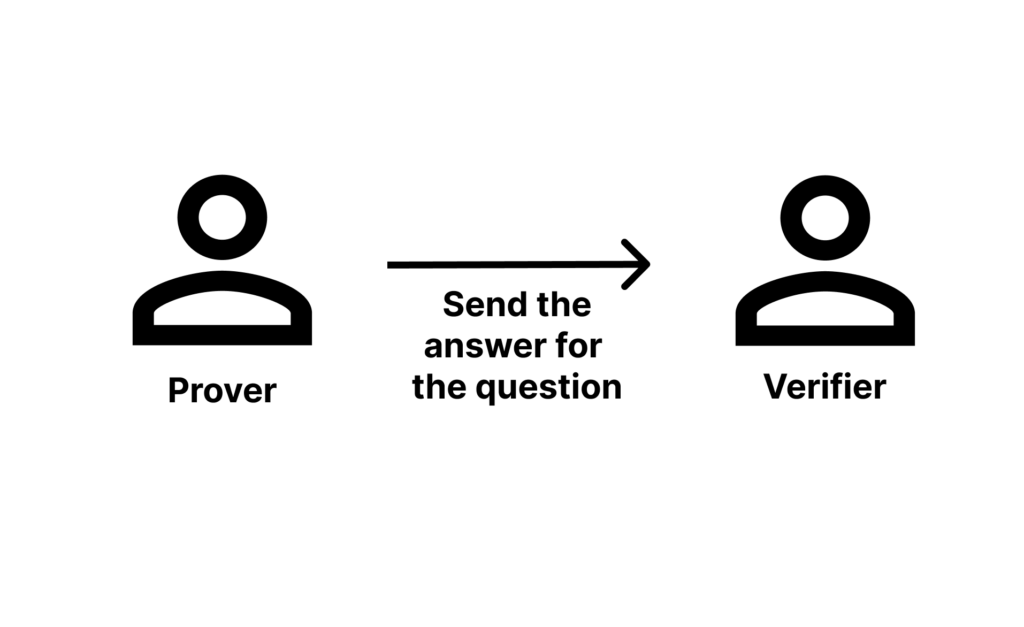
Fig: The prover calculates the answer and sends it to the verifier.
A color-blind friend and two balls – an example
Let us look at an example to understand this better. This is a really popular experiment introduced by Mike Hearn and Konstantinos Chalkias. Imagine you have a friend who is color blind and two balls of the same size, one red, and the other green. But your friend thinks both balls are the same and doubts your statement. You have to prove to him that the balls are different without actually telling him which is which.
Your friend hides the balls behind his back and selects one at random to show you. He does this repeatedly, and every time he asks you if it was the same ball as before, i.e., were the balls switched or not? Since you aren’t colorblind, you can definitely tell if he switched the ball or not. If the balls were of the same color, your probability of answering correctly would be 50%. After repeating this process “n” times, your friend would be convinced.
The probability of anticipation would become zero, and you would have achieved the three zero-knowledge properties. But in order to preserve “Zero-Knowledge,” your friend must not know which is green and which is red.
Types of Zero Knowledge Proofs
- Interactive zero-knowledge proof
- Non-interactive zero-knowledge proof
Interactive ZKP
This would require interactions between peers or computer systems. By means of interacting, the prover can prove the knowledge, while the validator can validate the same. This is the most typical scenario for ZKP. Though this is one of the best privacy protocols, it requires a lot of effort to prove. This also requires an interactive response from the verifier, which could be in any form (questions, challenges, etc.). Hence, interactive ZKP is more efficient for a smaller number of participants compared to a large group.
Non-interactive ZKP
This would be used to verify one’s statement to a larger group of people. If the prover is unable to prove it in the first place and cannot find a trusted verifier, this would be the last resort. This protocol is the basis for how zKSnarks (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) are built. zKSNARKS is the backbone of the ZCash protocol (a blockchain project based on Zero Knowledge Proof).
Ali Baba cave protocol (to prove Interactive ZKP)
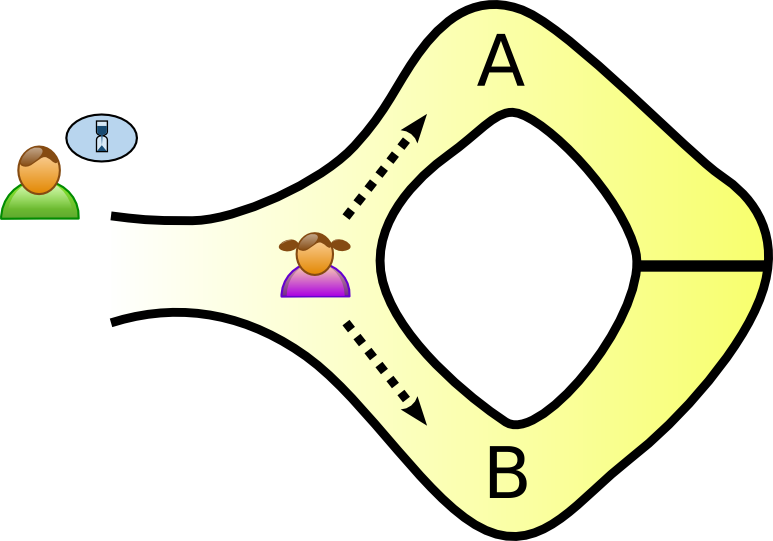
Fig: Ali Baba cave protocol
Assume a cave has a door on the opposite end, and only Alice knows the secret code to open the door. Alice wants to prove to Bob that she knows the secret without revealing it to him.
- Alice enters the cave and can take either path A or path B
- Alice takes path B. Bob asks Alice to exit using path B
- As Alice knows the secret to opening the door, she exits via path B.
Now, the probability that Alice didn’t open the door on the path chosen by Bob is 50%, indicating that it is easy to fool Bob. This exercise is repeated “n” times with different paths to reduce trustlessness.
Where can ZKPs be used?
- Messaging
End-to-end encryption is necessary in order to ensure no one reads your private messages except the intended person. This requires users to verify their trust in the server and vice versa. ZKPs can provide end-to-end trust without giving out extra information.
- Security of sensitive information
Sensitive information such as bank statements and credit card information requires an extra layer of protection, which could be provided by ZKPs.
- File System Control
Everything within a file system can be protected by ZKPs. The files, the users, and every login can have different layers of security.
Are ZKPs really important?
Zero Knowledge Proofs have proven to be capable of handling enterprise-level business security. Public ledgers provide anonymity with the help of addresses, but these addresses can be traced. Also, when it comes to storing or exchanging sensitive information, ZKPs have an added benefit. ZKPs can not only improve blockchains; they have also been proven useful otherwise.
Zero-knowledge proofs are like the knight in shining armor of the blockchain ecosystem, providing the ultimate privacy and making it secure for everyone to use.